
On Tuesday the 11th of June 2019 took place the very first Cloud Native Day in Montréal, an initiative by Archy and Carol from CloudOps (and with some support from the Cloud Native Foundation) that attracted approximately 300 people.
Here are some notes I gathered from this very interesting 1 day conference.
Archy started the day sharing (as he usually does during Kubernetes meetups) some Kubernetes and CNCF news : Kubecon North America 2020 Boston and Kubecon Europe Amsterdam locations were announced.
Contents
- 1 CNCF Open Policy Agent, openmetrics, opentelemetry by Luc Perkins from CNCF
- 2 Kubernetes Federation by Ian D. Crosby
- 3 Running Kafka on Kubernetes by Victor Gamov
- 4 Ville de Montréal Kubernetes usage
- 5 Rook and Ceph by Raymond Maika & Moh Ahmed
- 6 And few other talks : mainly about security
- 7 Containerization tips heard at the conference
CNCF Open Policy Agent, openmetrics, opentelemetry by Luc Perkins from CNCF
The first speaker was Luc Perkins from CNCF and he introduced to the audience the Open Policy Agent (opa) – among other things he explained that the policy language is a DSL named Rego, accessible via CLI and via a REST API to apply rules to your cluster.
Luc then talked about opentelemetry.io (opentracing from CNCF and opencensus from Google merged), focused on tracing for now; and then he mentioned openmetrics.io (basically prometheus standardized), that seems to be a bit stalled though.
Luc went on to explain the service mesh interface : cooperation between istio, linkerd, consul connect, etc. It’s a common set of kubernetes resources with 3 primary traffic domains: access control, split and metrics (maybe in the future the we will be able to use kubectl traffic ?)
Luc finished his presentation telling the CNCF is hardening specifications; he quoted Chris Aniszczyk with Kubernetes aiming to be the « POSIX layer for the cloud ».
Kubernetes Federation by Ian D. Crosby
Ian D. Crosby from Container Solutions told us about Kubernetes federation (he detailed how he linked a Kubernetes cluster running in the AWS Beijing region with a Kubernetes cluster running in the AWS Singapore region); he encountered few issues though (some root access was required by the federation component); and now v1 of federation is deprecated! That’s the risk you take with early technology !
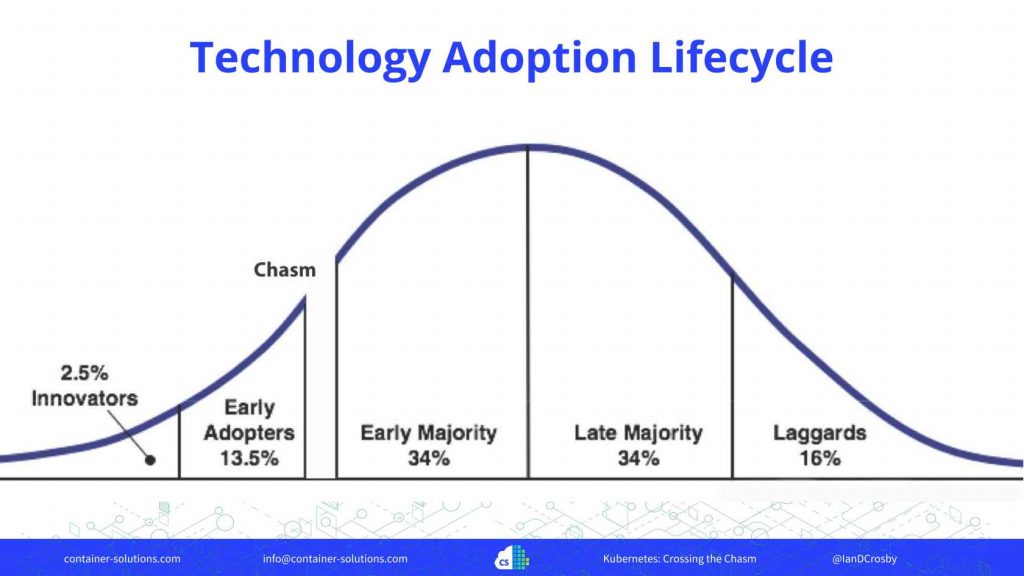
He then answered the question « Did Kubernetes cross the chasm? » Yes it did !
He then asked the question « How can you run a multi-tenant Kubernetes cluster ? » You can use network policy to isolate namespaces, then you can apply resource limits, and then apply RBAC too. That’s fine for starters: it will be cheaper and will require less operations – but having separate clusters will give you higher security, geographic coverage, smaller outage risk, etc.
To audit changes in configuration, and move fast, gitops (declarative configuration applied automatically) allows you to review that latest changes did not break security rules.
Ian mentioned Rook and OpenEBS for running stateful applications.
According to Ian, Kubernetes is becoming boring (focus is now mainly on security and reliability) – but that was the point!
Running Kafka on Kubernetes by Victor Gamov
Victor from Confluent, talked about running Kafka on k8s : you can use Helm charts to install the dependencies, then with a kubectl add-on, and a Kafka operator (made by confluent, to come soon) you can fully manage Kafka upgrades and also monitor Kakfa.
Ville de Montréal Kubernetes usage
Morgan Martinet & Marc Khouzam introduced to us (in french, yay!) how Ville de Montreal is using Jenkins as the source of truth (using Jenkinsfile) for gitops of all their (400) projects.
They (the platform architects) let developers create new git repositories from a Jenkins job.
Then, the developers generate a project skeleton (including a Dockerfile) with a yoman cli (« Is your project based on NodeJS », « Does your project requires an Oracle DB », etc. ) and then add it to the git repo previously created.
For logging, they preferred using Graylog rather than Elastic Search, apparently because it allowed them to stream the logs.
For monitoring their infra, they mentioned using the Prometheus black box exporter.
Among their challenges, they mentioned the need for Prometheus long term storage to store more than 14 days worth of monitoring data.
They also mentioned the difficulty of maintaining their custom solutions to bootstrap projects; buildpacks.io did not exist when they started, so that explains why.
You can find out more about how Ville de Montreal uses Kubernetes in this CNCF case study.
Rook and Ceph by Raymond Maika & Moh Ahmed
Rook can be seen as a storage orchestrator, deployed as an operator with its own CRDs.
Ceph acts as a backend, with 1 OSD (object storage daemon) per disk.
CSI: it is the spec for storage.
And few other talks : mainly about security
James Munnelly, talked about the cert manager and its next features (creating certificate authorities and signing certificates is not something many people are interested in, cert manager aims at making those tasks the most automated way possible); Don Bowman exposed how unsecured many Docker images and Helm charts are (always check the source before running those !); finally Ian Rae from CloudOps closed the conference with some humble words « I did not believe in Solaris zones and containerization 10 years ago ». Well … who did at that time ?!
Containerization tips heard at the conference
- To better secure your kubernetes workloads, make sure to set
runAsRoot: falseunder spec/containers. docker build -rmto not keep the transient layers on the machine running the daemon (helps save some disk space !).